Penetration testing normally evaluates a system’s ability to protect
its networks, applications, endpoints and users from external or
internal threats. It also attempts to protect the security controls and
ensures only authorized access.
Penetration
tester usually begins by gathering as much information about the target
as possible. Then he identifies the possible vulnerabilities in the
system by scanning. After which he launches an attack. Post-attack he
analyses each vulnerability and the risk involved. Finally, a detailed
report is submitted to higher authorities summarizing the results of the
penetration test.Penetration testing can be broken
down into multiple phases, this will vary depending on the organization
and the type of penetration test.
Let’s discuss each phase:
Reconnaissance & Planning
The
first phase is planning. Here, the attacker gathers as much information
about the target as possible. The data can be IP addresses, domain
details, mail servers, network topology, etc. In this phase, he also
defines the scope and goals of a test, including the systems to be
addressed and the testing methods to be used. An expert penetration
tester will spend most of the time in this phase, this will help with
further phases of the attack.
Scanning
Based
on the data collected in the first step, the attacker will interact
with the target with an aim to identify the vulnerabilities. This helps a
penetration tester to launch attacks using vulnerabilities
in the system. This phase includes the use of tools such as port
scanners, ping tools, vulnerability scanners, and network mappers.
While testing web applications, the scanning part can be either dynamic or static.
- In static scanning, the aim is to identify the vulnerable functions, libraries, and logic implementation
- Dynamic
analysis is the more practical way of scanning compared to static
analysis where the tester will pass various inputs to the application
and record the responses
Actual Exploit
This
is the crucial phase that has to be performed with due care. This is
the step where the actual damage is done. Penetration Tester need to
have some special skills and techniques to launch an attack on the
target system. Using these techniques an attacker will try to get the
data, compromise the system, launch dos attacks, etc. to check to what
extent the computer system or application or a network can be
compromised.
Risk Analysis & Recommendations
After
the penetration test is complete, the final goal is to collect the
evidence of the exploited vulnerabilities. This step mostly considers
all the steps discussed above and an evaluation of the vulnerabilities
present in the form of potential risks. Sometimes, in this step
pen-tester also provides some useful recommendations to implement in
order to improve security levels.
Report Generation
Now,
this is the final and the most important step. In this step, the
results of the penetration test are compiled into a detailed report.
This report usually has the following details:
- Recommendations made in the previous phase
- Vulnerabilities that were discovered and the risk levels they posses
- Overall summary of the penetration test
- Suggestions for future security
These
phases may sometimes vary depending on the organization and the type of
penetration test being conducted. This ‘What is Penetration Testing?’
article further explores different Penetration Testing types.
What are different types of Penetration Testing?
Penetration
testing can be categorized based on different parameters like the
knowledge of the target or the position of the penetration tester or the
areas where it is performed.
Penetration testing types based on knowledge of the target:

Black Box
When
the attacker has no knowledge of the target, it is referred to as a
black box penetration test. This type requires a lot of time and the pen
tester uses automated tools in order to find vulnerabilities and weak
spots.
White Box
When
the penetration tester is given the complete knowledge of the target,
it is called as white box penetration test. The attacker has complete
knowledge of the IP addresses, controls in place, code samples,
operating system details etc. It requires less time when compared to
black box penetration testing.
Grey Box
When
the tester is having partial information about the target, it is
referred to as gray box penetration testing. In this case, the attacker
will have some knowledge of the target information like URLs, IP
addresses, etc., butwill not have complete knowledge or access.
Penetration testing types based on the position of tester:
- If the penetration test is conducted from outside the network, it is referred to as external penetration testing
- Suppose, the attacker is present inside the network, simulation of this scenario is referred to as internal penetration testing
- Targeted testing is usually performed by the organization’s IT team and the Penetration Testing team working together
- In a blind penetration test, the penetration tester is provided with no prior information except the organization name
- In a double-blind test, at max, only one or two people within the organization might be aware that a test is being conducted
Penetration testing types based on where it is performed:
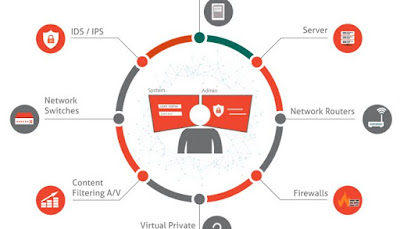
Network Penetration Testing
Network Penetration Testing activity aims at discovering weaknesses and vulnerabilities related to the network infrastructure
of the organization. It involves, firewall configuration & bypass
testing, Stateful analysis testing, DNS attacks etc. Most common
software packages which are examined during this test include:
- Secure Shell(SSH)
- SQL Server
- MySQL
- Simple Mail Transfer Protocol(SMTP)
- File Transfer Protocol
Application Penetration Testing
In Application Penetration Testing, penetration tester checks, if any security vulnerabilities or weaknesses are discovered in web-based applications.
Core application components such as ActiveX, Silverlight, and Java
Applets, and APIs are all examined. Therefore this kind of testing
requires a lot of time.
Wireless Penetration Testing
In
Wireless Penetration Testing, all of the wireless devices which are
used in a corporation are tested. It includes items such as tablets,
notebooks, smartphones, etc. This test spots vulnerabilities in terms of
wireless access points, admin credentials, and wireless protocols.
Social Engineering
Social Engineering
Test involves attempting to get confidential or sensitive information
by purposely tricking an employee of the organization. You have two
subsets here.
- Remote testing – involves tricking an employee to reveal sensitive information via an electronic means
- Physical testing – involves the use of a physical means to gather sensitive information, like threaten or blackmail an employee
Client Side Penetration Testing
The
purpose of this type of testing is to identify security issues in terms
of software running on the customer’s workstations. It primary goal is
to search and exploit vulnerabilities in client-side software programs.
For example, web browsers (such as Internet Explorer, Google Chrome,
Mozilla Firefox, Safari), content creation software packages (such as
Adobe Framemaker and Adobe RoboHelp), media players, etc.
So,
these are different types of penetration test based on different
parameters. Now, in the remaining of this ‘What is Penetration Testing?’
article we will talk about the tools that a penetration tester can use
to conduct a penetration test.
What tools are used for Penetration Testing?
Penetration
testers take the aid of different kinds of penetration tools to make
the penetration test much faster, efficient, easy, and reliable. There
are a lot of popular Penetration Testing tools, where most of them are
free or open source software. Some of the most widely used pen testing
tools include:
- Nessus – It is a network and
web application vulnerability scanner, it can perform different types of
scans and help a penetration tester identify vulnerabilities.
- Metasploit
– It is an exploitation framework that has been packed with various
capabilities. A skilled attacker can generate payloads, shellcodes, gain
access, and perform privilege escalation attacks using Metasploit.
- Nmap or network mapper is a port scanner that scans systems and networks for vulnerabilities linked to open ports.
- Wireshark – It is a tool for profiling network traffic and for analyzing network packets.
Apart from the above ones, there are others like John the Ripper, Burp Suite, Cain and Abel, and many more popular tools.
Well,
we have reached the end of this article. So, know you know what is
Penetration Testing, its phases, types, and tools. So, if you are
curious as to how to perform penetration testing using Metasploit
Framework, you can refer to the Penetration Testing Tutorial video
below.
Knowing about risks on the internet and how they can be prevented is
very useful, especially as a developer. Web hacking and penetration
testing is the v2.0 of self-defense! But is knowing about tools and how
to use them really all you need to become a pen tester? Surely not. A
real penetration tester must be able to proceed rigorously and detect
the weaknesses of an application. They must be able to identify the
technology behind and test every single door that might be open to
hackers.
This repository aims first to establish a reflection method on
penetration testing and explain how to proceed to secure an application.
And secondly, to regroup all kind of tools or resources pen testers
need.
Be sure to know basics of programming languages and internet security before learning pen testing.
Also, this is important to inform yourself about the law and what you
are allowed to do or not. According to your country, the computer laws
are not the same. First, check laws about privacy and surveillance:
Nine eyes countries,
Five eyes
and Fourteen Eyes. Always check if what you're doing is legal. Even
when it's not offensive, information gathering can also be illegal!




Comments
Post a Comment